this article you can use with link LibyaSOS - PLEASE RESPECT OUR TIME - THANKS
“We get information from open sources on the Internet, we get Twitter,” British Wing Commander Mike Bracken told AFP. Another NATO official attested, “Twitter is a great source."
“We get information from open sources on the Internet, we get Twitter,” British Wing Commander Mike Bracken told AFP. Another NATO official attested, “Twitter is a great source."
Really?!?!
Nato sources said Libyan rebels tweeting from the rebel city of Misurata, as well as Ajdabiya and Tripoli, were providing valuable updates on the movements of troops, military vehicles and civilians.
Really?!?!
Libya Traffic Divided by Worldwide Traffic
Really!??
These days, with Facebook and Twitter and social media galore, it can be increasingly hard to tell who your "friends" are.
Army of Fake Social Media Friends to Promote Propaganda
It's recently been revealed that the U.S. government contracted HBGary Federal for the development of software which could create multiple fake social media profiles to manipulate and sway public opinion on controversial issues by promoting propaganda. It could also be used as surveillance to find public opinions with points of view the powers-that-be didn't like. It could then potentially have their "fake" people run smear campaigns against those "real" people. As disturbing as this is, it's not really new for U.S. intelligence or private intelligence firms to do the dirty work behind closed doors.
EFF previously warned that Big Brother wants to be your friend for social media surveillance. While the FBI Intelligence Information Report Handbook (PDF) mentioned using "covert accounts" to access protected information, other government agencies endorsed using security exploits to access protected information.
----------------------------------
Libyan Twitterati send off tweets about Gadhafi’s latest depravities at a frenetic pace. Tweets containing links to uploaded video, like this one — which, fair warning, is graphic — clearly show the roads that Gadhafi’s troops use to travel.
----------------------------------
Really?!? Video?!?
It's not a big surprise that the U.S. military also wants to use social media to its benefit. The Air Force used the chart below to show how social media influences public opinion.
http://www.youtube.com/user/miusrata17miusrata
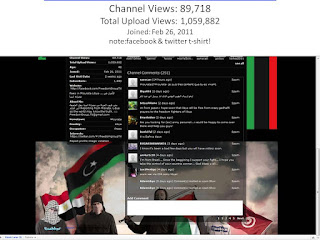
Channel Views: 89,718 / Total Upload Views: 1,059,882 / Joined: Feb 26, 2011
note:facebook & twitter t-shirt!
Channel Views: 89,718 / Total Upload Views: 1,059,882 / Joined: Feb 26, 2011
note:facebook & twitter t-shirt!
The 6th Contracting Squadron at MacDill Air Force Base sought the development of Persona Management Software which could be used for creating and managing fake profiles on social media sites to distort the truth and make it appear as if there was a generally accepted agreement on controversial issues. "Personas must be able to appear to originate in nearly any part of the world and can interact through conventional online services and social media platforms." What happened to don't lie and the Uniform Code of Military Justice?
Everything revealed after Anonymous leaked emails from private security firm HBGary Federal is disturbing on many levels. However, the Daily Kos said with the Persona Management Software it would take very few people to create "an army of sockpuppets" which could distort the truth while appearing to be "an entire Brooks Brothers riot online." more -->
In another document unearthed by "Anonymous," one of HBGary's employees also mentioned gaming geolocation services to make it appear as though selected fake persons were at actual events.
Government involvement
Eerie as that may be, more perplexing, however, is a federal contract (PDF) from the 6th Contracting Squadron at MacDill Air Force Base, located south of Tampa, Florida, that solicits providers of "persona management software." Update: The contract has since been taken off FBO.gov. The link above has been updated.
While there are certainly legitimate applications for such software, such as managing multiple "official" social media accounts from a single input, the more nefarious potential is clear.
----------------------------------
"We don't see something on Twitter and go and drop bombs," Mike Bracken said. "We never act on a single source. It's more complex." He refused to discuss which accounts analysts followed.
----------------------------------
Unfortunately, the Air Force's contract description doesn't help dispel suspicions. As the text explains, the software would require licenses for 50 users with 10 personas each, for a total of 500. These personas would have to be "replete with background , history, supporting details, and cyber presences that are technically, culturally and geographacilly consistent."
http://www.youtube.com/profile?user=miusrata17miusrata&view=subscribers&start=480
Who are subscribers?
Who are subscribers?
Channel Views: 89,718 / Total Upload Views: 1,059,882 / Joined: Feb 26, 2011
software would require licenses for 50 users with 10 personas each, for a total of 500
It continues, noting the need for secure virtual private networks that randomize the operator's Internet protocol (IP) address, making it impossible to detect that it's a single person orchestrating all these posts. Another entry calls for static IP address management for each persona, making it appear as though each fake person was consistently accessing from the same computer each time.
Channel Views: 89,718 / Total Upload Views: 1,059,882 / Joined: Feb 26, 2011
The contract also sought methods to anonymously establish virtual private servers with private hosting firms in specific geographic locations. This would allow that server's "geosite" to be integrated with their social media profiles, effectively gaming geolocation services.
The Air Force added that the "place of performance" for the contract would be at MacDill Air Force Base, along with Kabul, Afghanistan and Baghdad. The contract was offered on June 22, 2010.
It was not clear exactly what the Air Force was doing with this software, or even if it had been procured.
Though many questions remain about how the military would apply such technology, the reasonable fear should be perfectly clear. "Persona management software" can be used to manipulate public opinion on key information, such as news reports. An unlimited number of virtual "people" could be marshaled by only a few real individuals, empowering them to create the illusion of consensus. more -- >
----------------------------------
In the early days of the Libya war, U.S. commanders were adamant that they didn’t communicate with the Libyan rebels about what targets to bomb. As it turns out, they don’t need to. They’ve got Twitter.
----------------------------------
READ ALSO:
NATO-MATRIX or DISNEYLAND (part I) Fake profiles--> http://libyasos.blogspot.com/2011/06/nato-matrix-or-disneyland.html
NATO-MATRIX or DISNEYLAND (part II) Crime on Twitter -- > http://libyasos.blogspot.com/2011/06/nato-matrix-or-disneyland-part-ii.html